meet the New England IT team you can rely on














We love conversations with our clients but it's our work that does the real talking.
“We needed help it was only a phone call away”
“We enjoyed another successful year at Hoag Library in no small part due to our relationship with Info Advantage. With the help of Johnathan and Linda we replaced many of our computers this year and have finally gotten all of our equipment onto a three year cycle for replacement. The installation of the new computers was handled in house knowing that if we needed help it was only a phone call away. Jeremiah was instrumental in helping us get all of the new equipment online and swapping out some other equipment with items that were at the end of life. Other times we have depended on Jacob to help us figure out why we were having problems. (an unknown power outage was one cause.) and he and Kris reset programs when we could not make successful updates. We were also unable to catalog new books when the dedicated computer went down. We sent the computer to IA , they performed “magic” and Jacob returned it and reinstalled it until our new computers came in.”

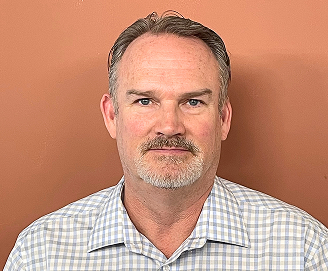
BETTY SUE MILLER
Director Hoag Library
“Words can’t describe the difference Info Advantage has made."
“I have been working with the Info Advantage team for a little over a year now as the IT Manager for VP Supply Corp. Words cannot describe the difference Info Advantage has made in my ability to do my job and protect our network and information assets. What started as a hardware vendor has now evolved into providing MSSP services to better protect our network – and we could not be happier with the quick return on investment this has given us. I would like to give a special shout-out to the members of the Info Advantage team who have not only done their job exceptionally well but have also mastered the soft skills and make me feel as though I can always reach out if we need them. Johnathan, Chris Chan, Chris McDonald, and Nick Wetherwax have been outstanding over the past year. With continued success like this VP Supply will have Info Advantage as a partner for many, many years to come!”

ADAM DEKRAMER
IT Manager VP Supply Corp
“I’ve worked with Info Advantage for 12 yrs. across multiple companies.”
“I have worked with Info Advantage over the past 12 years at a couple of companies. This year, Info Advantage helped me deploy a new VMWare / EMC environment for my current employer. During the selection process, they were very responsive with quote changes, responses to questions and updates explaining every aspect of the roll-out. They were very willing to take my current level of knowledge into consideration in the quoting process and their quotes were very competitive. Once awarded the project, Info Advantage proceeded very quickly to order and install the hardware in agreed time with on-hands training and system documentation for me. I would personally recommend Info Advantage for any project.”

CLINT SCHWAB
Durst Imaging / Rochester, NY
iaGuardianMSP Solutions Builder
See what IT should actually cost your business. Use our calculator to estimate your monthly budget based on your team size, needs, and security requirements. Click the button to get your estimate.

Always On IT Services & Cybersecurity Protection for Rochester Businesses
We deliver managed IT services and cybersecurity solutions to Rochester Businesses that protect, ensure regulatory compliance, and minimize risk so you can operate with confidence and focus on what drives your success.
iaGuardian IT Services Suite

UC: Seamless Connectivity
Scalable, seamless communication that boosts collaboration and keeps teams connected.

MSP: Transform IT Challenges
24/7 support, strong security, and cost-effective IT transforming your technology challenges into growth.

DR: Business Continuity
Stay resilient. Prevent data loss and downtime with expert support and advanced recovery.

Cloud: Secure Agile. Efficient.
Secure, scalable access to apps and data—anytime, anywhere—with built-in efficiency and cost savings.

Secure: Elite Cyber Protection
Always-on threat detection and real-time human response to stop attacks before they spread.







Industries We Empower
With decades of hands-on experience across regulated and fast-moving industries, we understand the unique risks you face. Our deep industry expertise allows us to deliver cybersecurity-first, compliance-ready IT solutions tailored to your environment and built to protect what matters most.

Financial Service Organizations

Healthcare &
Medical

Manufacturing &
Distribution

Legal Firms &
Attorneys

Nonprofit
Organizations

Professional
Services
Industries We Empower
With decades of hands-on experience across regulated and fast-moving industries, we understand the unique risks you face. Our deep industry expertise allows us to deliver cybersecurity-first, compliance-ready IT services tailored to your environment and built to protect what matters most.
More Insights
Stay connected with all of the latest IT services trends and alerts by subscribing to our blog.

IT Onboarding & Offboarding: The Security Checklist SMBs Skip
Hiring a new employee feels productive.
An employee leaving feels administrative.
But from a security perspective, both moments are high-risk events.
And for many small businesses, they’re handled casually.
Most breaches don’t begin with sophisticated hackers forcing their way in.
They begin with access that was never configured correctly - or never removed at all.
That’s not a technology failure.
It’s a process failure.
Download the Checklist
Want to see exactly what should happen every time someone joins or leaves your company?
Download Info Advantage’s Onboarding & Offboarding Security Checklist HERE
(If it’s not written down, it won’t happen consistently.)
Why Onboarding and Offboarding Are IT Issues
In many SMBs, onboarding and offboarding sit with HR. IT gets notified eventually - sometimes days later.
That delay creates exposure.
During Onboarding
New hires receive excessive access “just in case”
Shared passwords are reused for convenience
Multi-factor authentication (MFA) is postponed to save time
Access is granted without documentation
The result? Over-permissioned users from day one.
During Offboarding
Accounts remain active “until someone gets to it”
Personal devices still sync company email
Shared credentials aren’t changed
No one verifies what access actually existed
None of this is malicious.
But it creates real, measurable risk.
The Risks Most Businesses Don’t See
Excessive Access
New employees often inherit access from the previous role holder. Over time, permissions stack. Systems evolve. Responsibilities shift.
No one reviews what’s still necessary.
This violates the principle of least privilege - and dramatically increases breach impact if credentials are compromised.
Delayed Access Removal
Even a few hours of lingering access can expose:
Client communications
Financial data
Internal documentation
Intellectual property
If a departure is unexpected or contentious, the risk multiplies.
Shared Credentials
If multiple people know the same password:
There is no accountability
There is no clean audit trail
There is no simple way to revoke access
Shared credentials eliminate control.
Compliance & Insurance Exposure
Cyber insurance carriers and regulatory frameworks increasingly expect:
Role-based access
Documented provisioning
Immediate deprovisioning
Failure to demonstrate this can complicate claims, audits, and renewals.
That’s not just a security issue.
It’s a business continuity issue.
What a Secure Process Actually Looks Like
You don’t need enterprise software or complex workflows.
You need clarity. Ownership. Consistency.
Onboarding Essentials
Create individual user accounts (never shared logins)
Assign access based strictly on job role
Enable MFA from day one
Enroll devices in management tools
Document what access was granted and why
Offboarding Essentials
Disable accounts immediately on the employee’s last day
Revoke access to email, file storage, VPN, and SaaS platforms
Reset any shared credentials
Recover or remotely wipe company devices
Confirm removal of third-party application access
Document completion
If it isn’t documented, it isn’t defensible.
Why This Matters More Than Ever
Remote work, cloud platforms, and SaaS adoption have changed the access model completely.
Employees no longer work inside a perimeter.
They work from everywhere.
Security now depends on identity and access control - not office walls.
Platforms like Microsoft 365 make access management significantly easier - but only when policies are enforced consistently.
The technology is mature.
The discipline must match it.
Start Small (That’s How This Works)
If this feels overwhelming, start with one operational improvement:
Implement a mandatory onboarding checklist
Implement a mandatory offboarding checklist
Establish a policy that access is role-based and time-bound
Assign ownership - someone is accountable every time
Perfection is not required.
Consistency is.
The Bottom Line
Onboarding and offboarding are not administrative tasks.
They are security controls.
When access is granted intentionally and removed immediately, you:
Reduce breach risk
Protect client trust
Strengthen compliance posture
Improve audit readiness
Protect insurance eligibility
At Info Advantage, we help small and mid-sized businesses implement secure, repeatable onboarding and offboarding processes - without slowing hiring or creating unnecessary friction.
Because the easiest breaches to prevent are the ones caused by missed steps.