Press Releases
Nick Wetherwax named 2026 Re:Gen Rising Honoree by Greater Rochester Chamber

Info Advantage Honors Life and Legacy of Beloved Brand Ambassador Captain Jack
Info Advantage's Linda Weller Named Finalist for 2026 TechRochester TWY Award
Info Advantage Named as 2026 Greater Rochester Chamber MWBE Award Honoree
Info Advantage Named to CRN's MSP 500 List for 2026
Linda Weller, IA Named 2026 ATHENA Organizational Finalist
Info Advantage Named to 2025 In The Lead: Best Women-Owned Business
Info Advantage Named a 2026 Elevating Women Award Winner
Info Advantage Hosts Women in IT Roundtable at Rochester Security Summit
IA to Participate in Woofstock 2025 to Support York, K9's in Blue and PAWS
IA Recognized Among Top 50 Fastest-Growing MWBE's by Chamber
IA Gives Back 2025 Raises $5,500 for REVS, Totaling Over $10,000 Combined
Linda Weller Among 2025 Women of Excellence Honorees by RBJ
Linda Weller Receives Ally in Action Award from MHA Rochester
IA Gives Back 2025 Raises Funds for REVS at 2nd Fundraising Event
Linda Weller Given Mastermind Partnership Award at Ingram ONE
IA Named to 2024 In The Lead: Best Women-Owned Business by RBJ
Info Advantage Raises $5,132 for REVS Through 2024 IA Gives Back Event
Info Advantage Hosts 2024 IA Gives Back Raffle Fundraiser for REVS
In The News

Showcasing our 2026 ATHENA Organizational Award Finalists

Dozens of Women Honored at 40th Athena Awards Ceremony
40th Annual ATHENA Awards Celebrate Excellence
2025 In The Lead: Best Women-Owned Business by RBJ
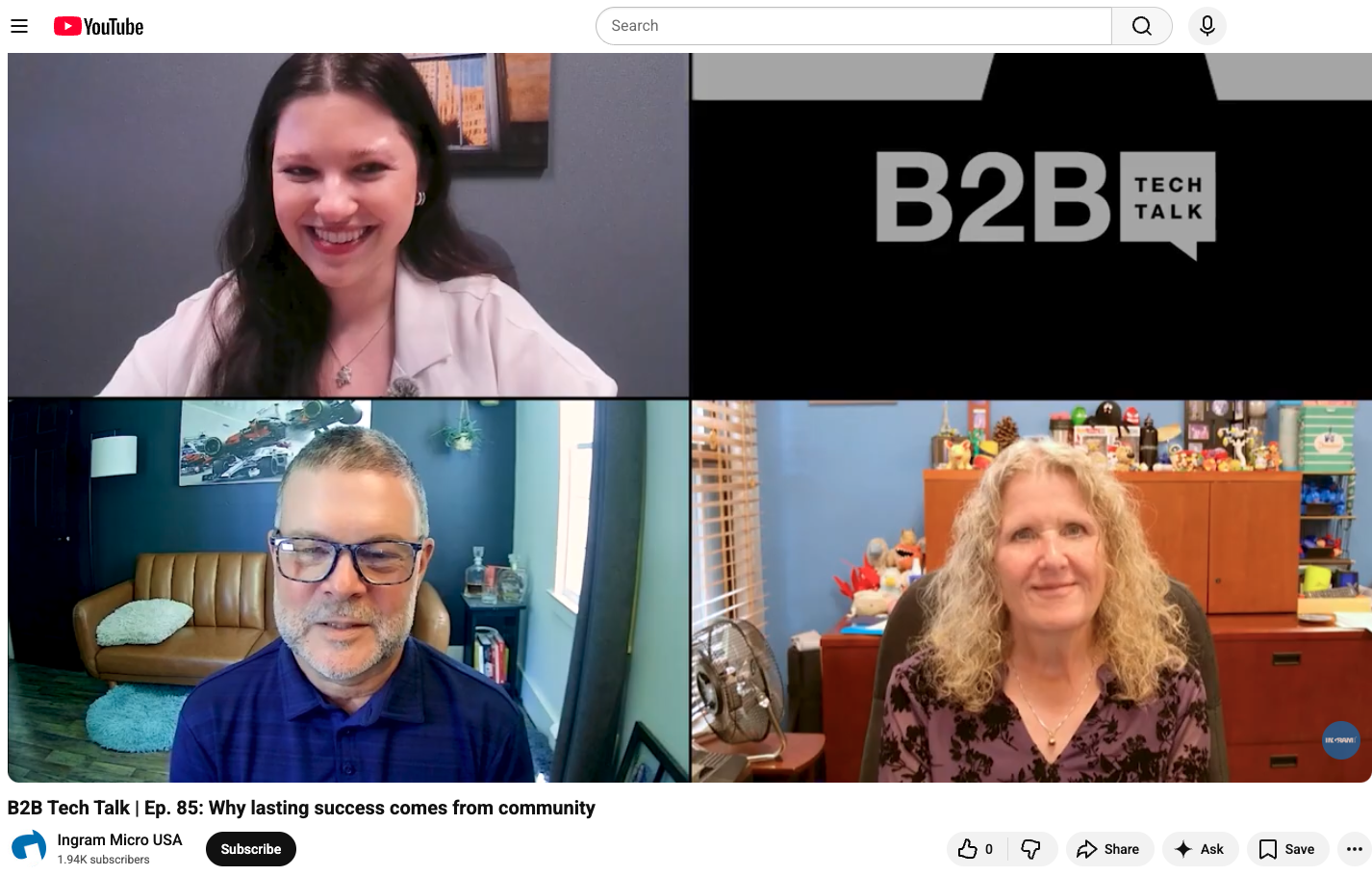
IA President Featured on B2B Tech Talk Podcast
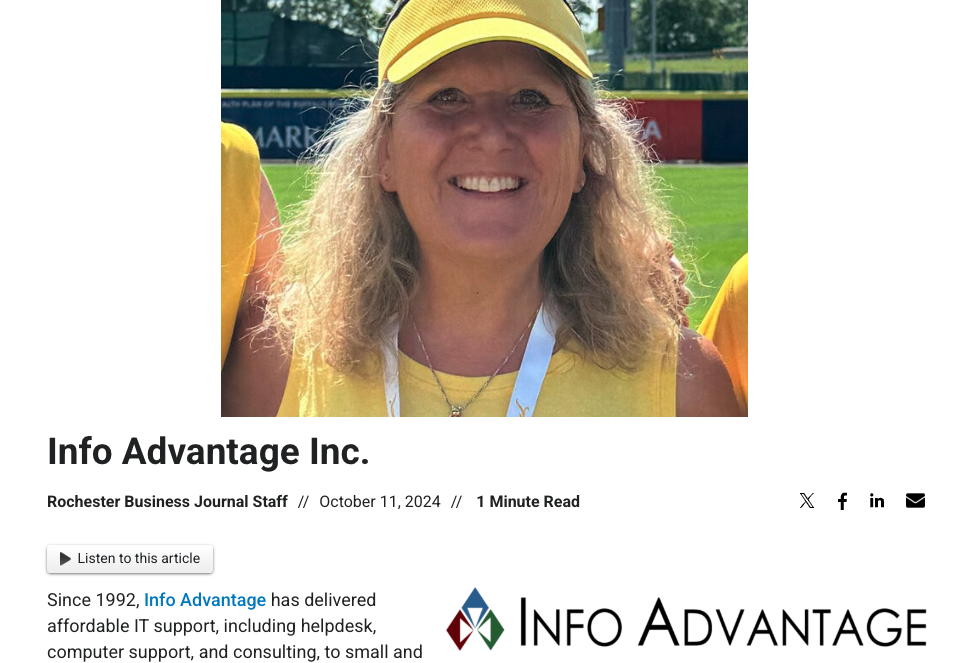
2024 In The Lead: Best Women-Owned Business by RBJ

WHY ROC: IA offers advice during Cyber Security Month
Info Advantage Shares Key Cybersecurity Tips

27 Complete Year-Long Leadership Orleans Program
Awards
2026
ATHENA Organizational Award Finalist
CRN's MSP500 List - Pioneer Category
Greater Rochester Chamber MWBE Award - Top 50
2025
Greater Rochester Chamber MWBE Award - Top 50 (35th)
MHA's Ally in Action Award - Linda Weller
Rochester Business Journal's Women of Excellence Award Honoree - Linda Weller
Rochester Business Journal's In The Lead: Best Women-Owned Business
Rochester Business Journal's Elevating Women Award
2024
Ingram Micro/Trust X Alliance Partner - Mastermind Partnership Award - Linda Weller
Rochester Business Journal's In The Lead: Best Women-Owned Business
2022
Rochester Business Journal's Women-Owned Business
2021
Rochester Business Journal's Women-Owned Business
2020
Rochester Business Journal's Women-Owned Business
One of the Largest IT Support Firms
2017
One of the Largest IT Support Firms
2016
One of the Largest IT Support Firms
Ingram Micro Women in Tech - Empowering Women Through Mentorship - Linda Weller
Largest Computer Company
2014
Largest Computer Company
Tech Tips
Downloads - Column
Cybersecurity: A Beginner’s Guide to Protecting Your Business
Get started with foundational cybersecurity practices that every business should implement to safeguard against common threats and minimize risk.
The Cybersecurity Toolkit for Small Businesses
A comprehensive toolkit of strategies, templates, and checklists tailored for small businesses to build a strong cybersecurity foundation.
The Incident Response Playbook: Be Prepared for Any Cyber Attack
Equip your team with a detailed playbook to quickly and effectively respond to security breaches, minimize damage, and keep your operations running smoothly.
Tools
Wireshark
A network protocol analyzer that captures and inspects data traveling through a network in real-time, helping identify vulnerabilities and troubleshoot network issues.
Metasploit
An open-source penetration testing framework that allows security professionals to test system defenses, find weaknesses, and improve security by simulating attacks.
Nmap (Network Mapper)
A network scanning tool used for discovering devices on a network, scanning for open ports, and identifying vulnerabilities, often used in network audits and security assessments.
Kali Linux
A Debian-based Linux distribution with a suite of pre-installed security tools for penetration testing, forensics, and reverse engineering, commonly used by cybersecurity professionals.



